THREE TOP CYBER FRAMEWORKS TO UNDERSTAND
Cyber security frameworks are documents that contain written guidelines, standards, and best practices that guide cybersecurity risk management. This framework’s work is to assist in reducing cyber security exposure. Frameworks make things easy. They act as a guidebook on protecting organizations from cyber-attacks. They have well-defined processes and procedures that guide them towards assessing, monitoring, and mitigating risks.
Here are the three top cyber frameworks:-
The NIST Cybersecurity Framework
It is the top most cybersecurity frameworks that protect critical infrastructures from cyber-attacks. The framework was formed during President Obama’s tenure. An executive order was declared by government to establish NIST Cybersecurity Framework to improve cybersecurity for critical infrastructure. It required the public and private sectors to work together so as to identify, assess and manage cyber risks.
NIST Cybersecurity Framework has grown to become the best framework that helps organizations towards protecting themselves from any attack by assessing, identifying security loopholes, and helping them meet cybersecurity regulations.
ISO/IEC 27001 and ISO 27002
It’s framework was developed by an international organization for standardization. It is a framework that certifies or validates most cybersecurity programs internationally and across third parties. Its main goal is to mitigate risk and help in eliminating already identified risks. With an ISO certification, companies feel they are doing the right thing up to the standards that are required in managing cyber risks. It is an indicator that the organization has matured cybersecurity practices and controls.
The two frameworks work hand in hand. They are interconnected. ISO 27000 builds foundations of information security and sets guidelines to help in the introduction and implementation of best practices while ISO 27002 implements control.
An organization having ISO 27001 certification benefits from improved customer trust. It also increases productivity.
SOC2
It is a cybersecurity framework developed by the American Institute of certified public Accountants (AICPA). It helps in verifying the security of vendors and their partners. It makes sure that the client’s data is well managed. It just ensures that service providers are managing data for clients and protecting the interest of the organization as well. Privacy for the client is paramount for SOC2. A guide is followed to manage customer data. SOC2 uses five trusted services principles. These are security, availability, processing integrity, confidentiality, and privacy.
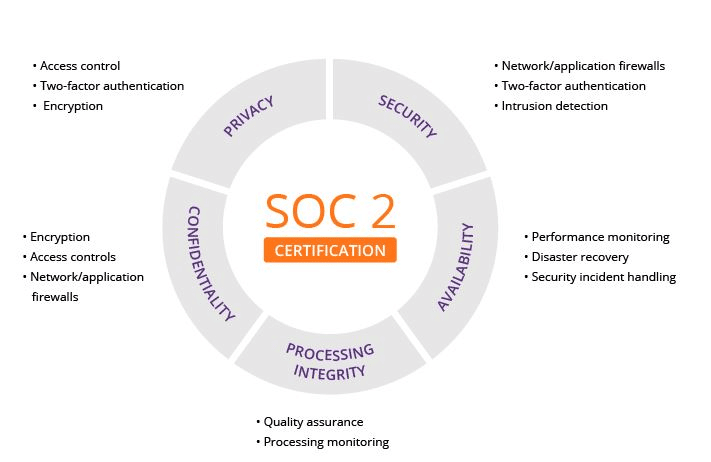
It has more than 60 compliance requirements and an auditing process that is supposed to be met by third-party systems and controls.